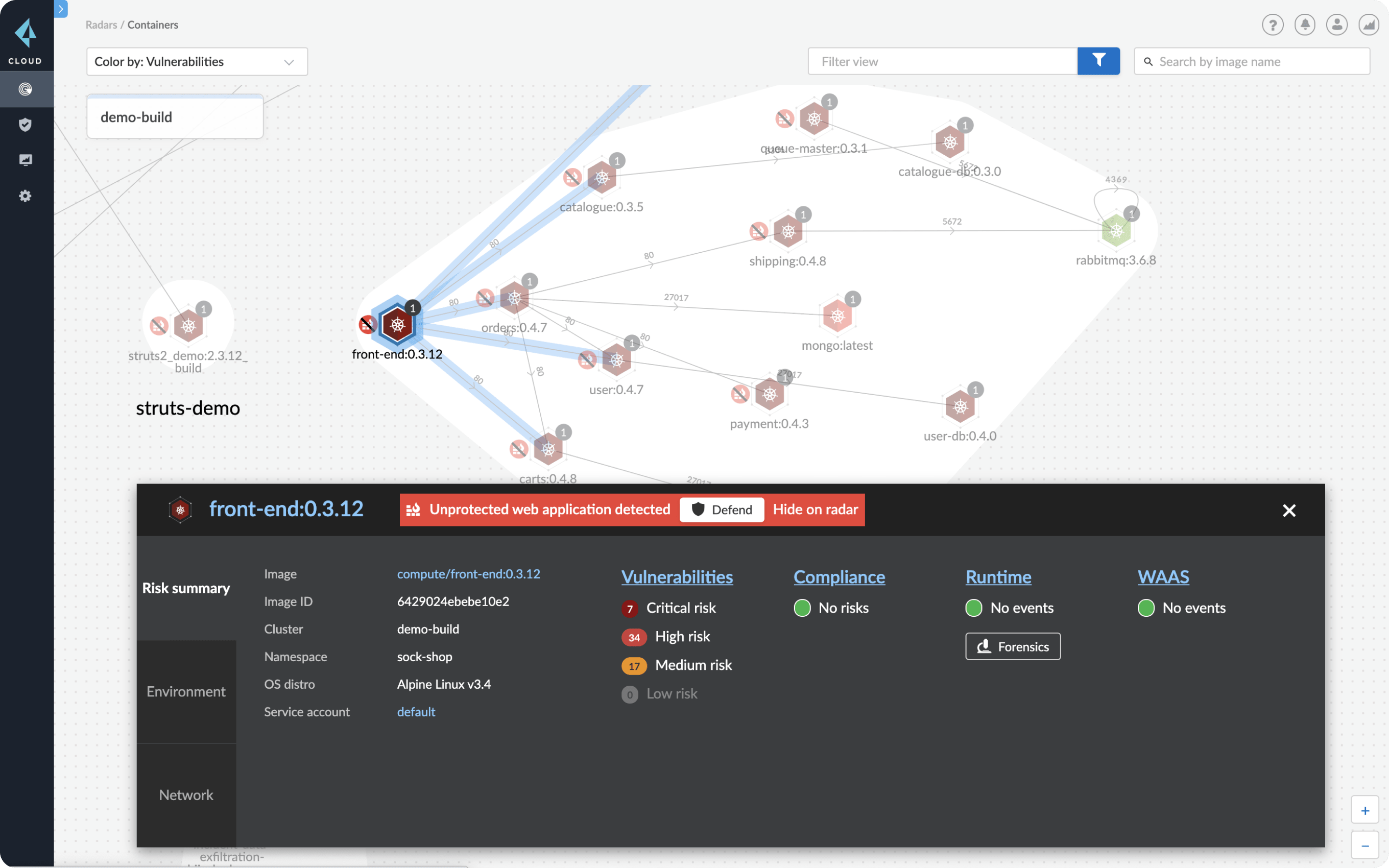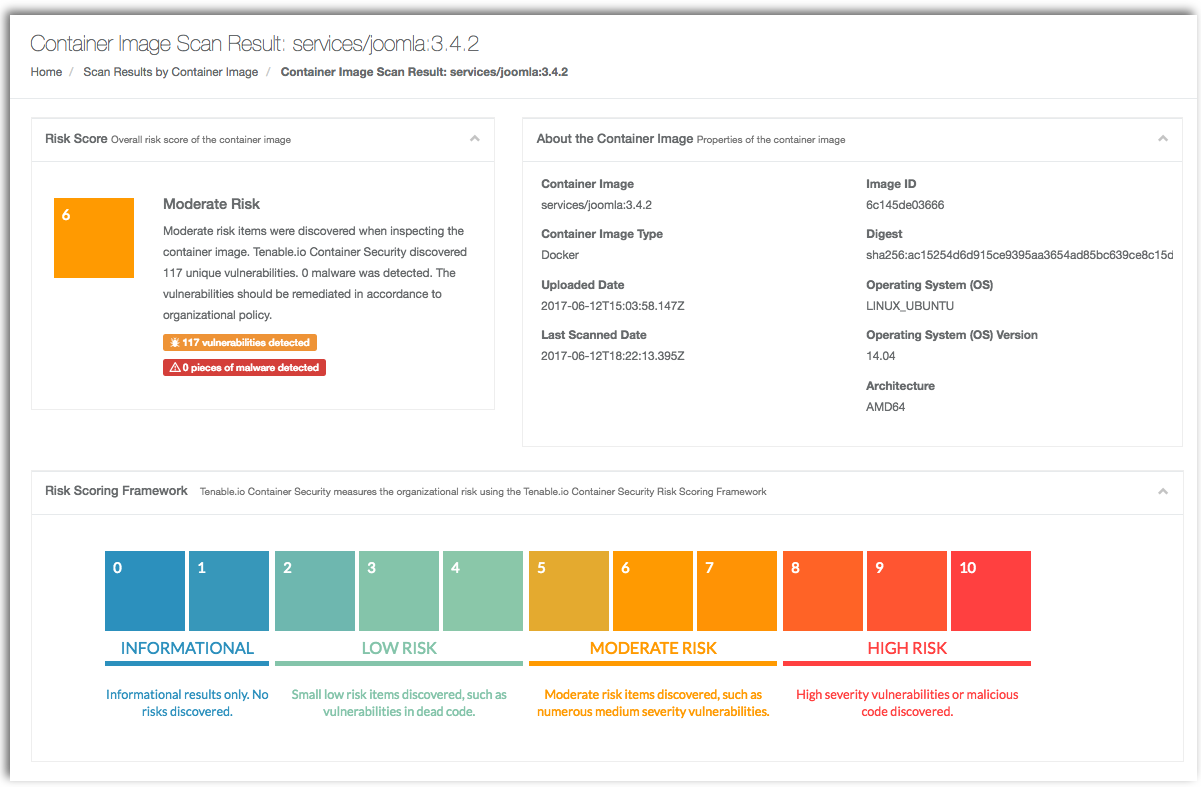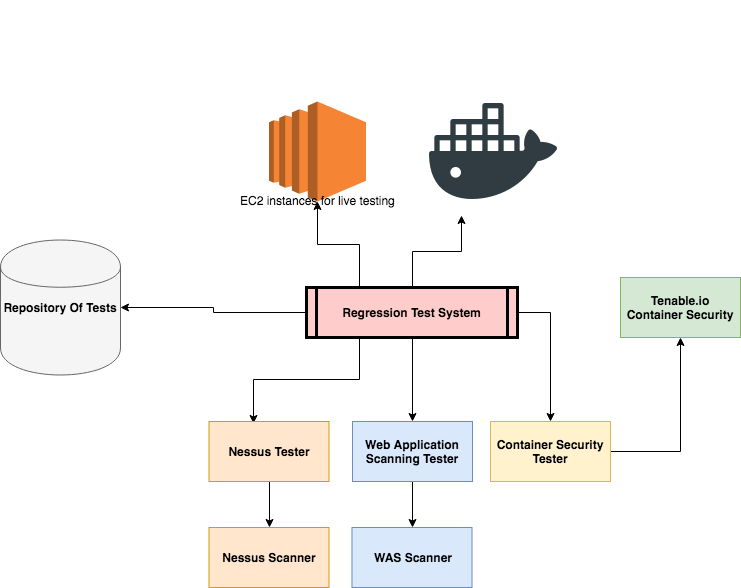
Automated Reconciliation of Vulnerability Detection Across Scan Engines | by Sasan Padidar | Tenable TechBlog | Medium

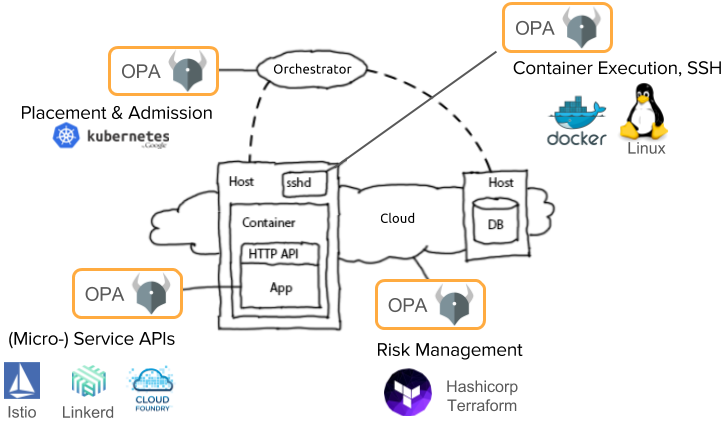
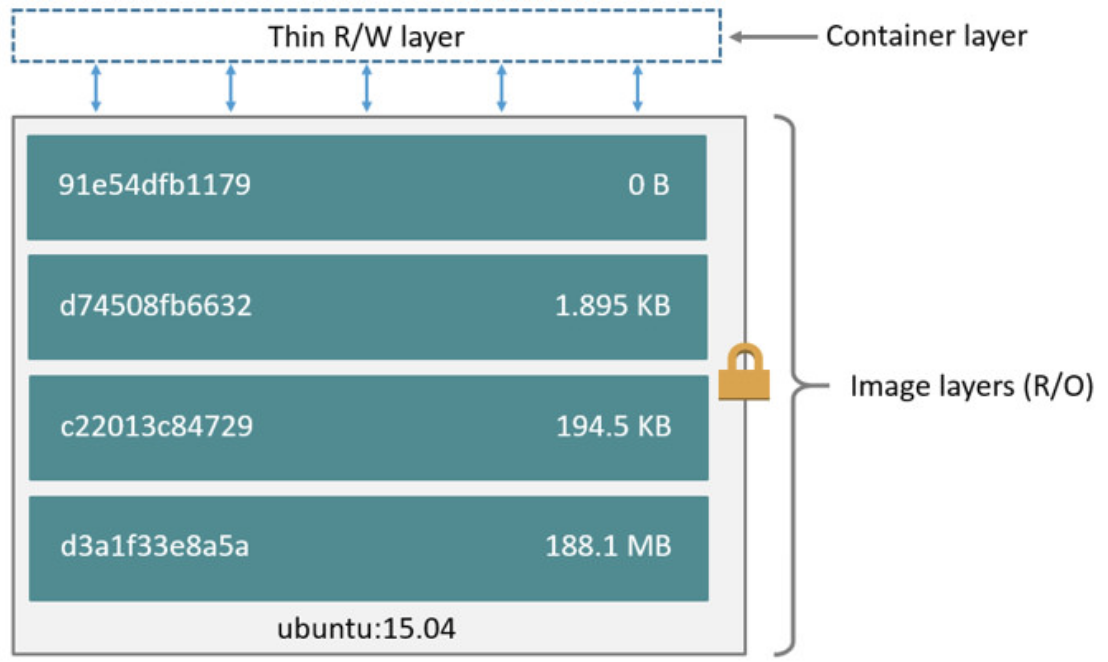
Operator best practices - Container image management in Azure Kubernetes Services (AKS) - Azure Kubernetes Service | Microsoft Docs

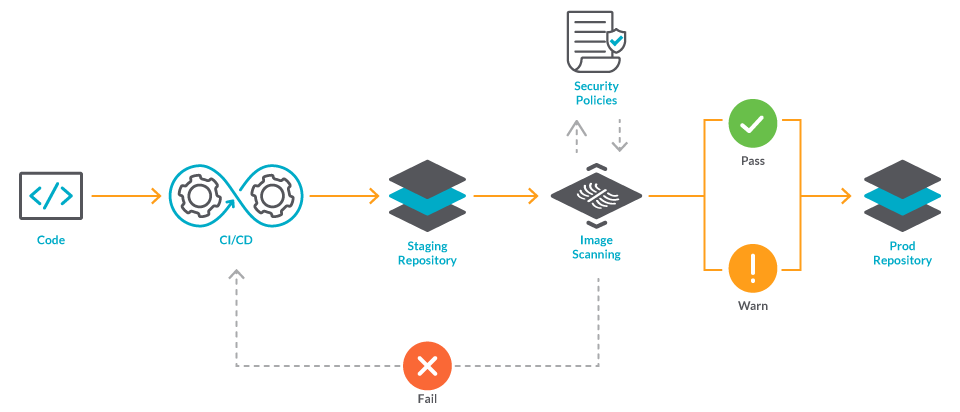
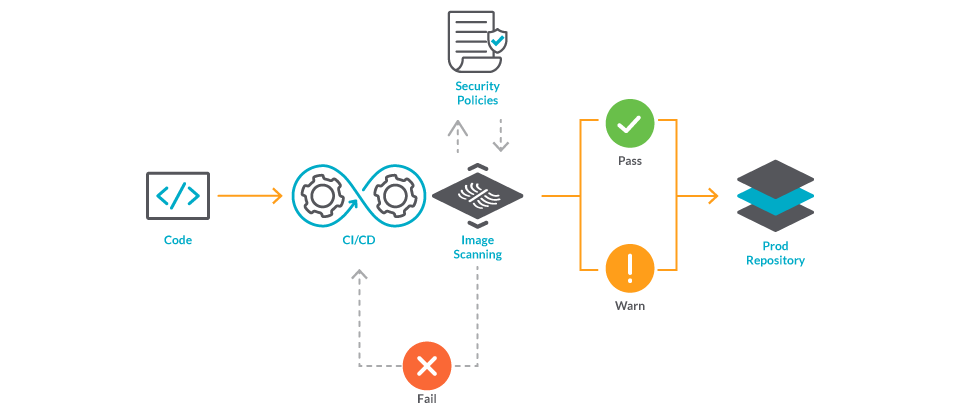
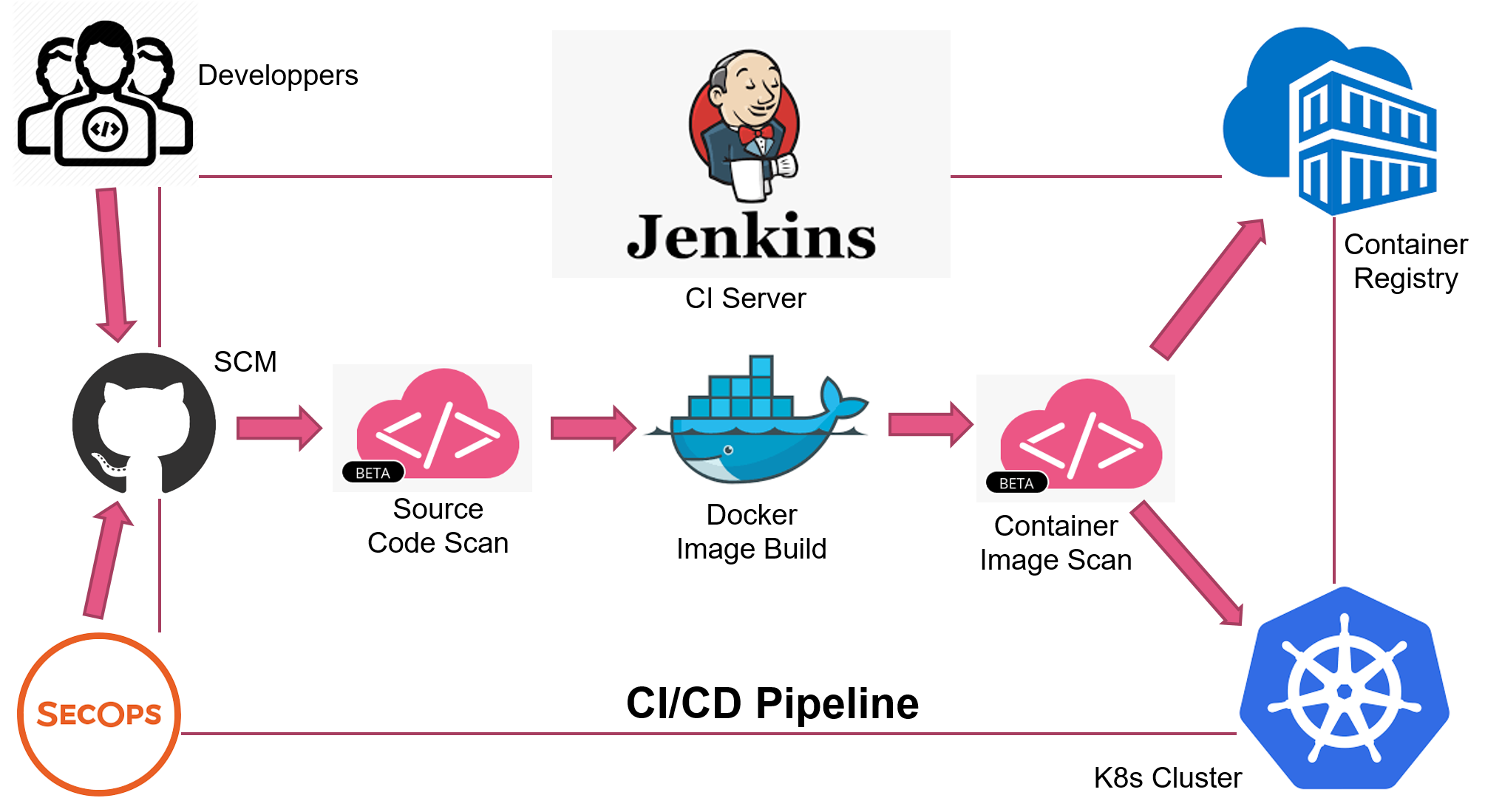
Adding Image Security Scanning to a CI/CD pipeline | by Larbi Youcef Mohamed Reda | alter way | Medium