![PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/ec6ca596b8a74e2a2c6a525fb9ccd3476c20eb3e/7-Figure6-1.png)
PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar
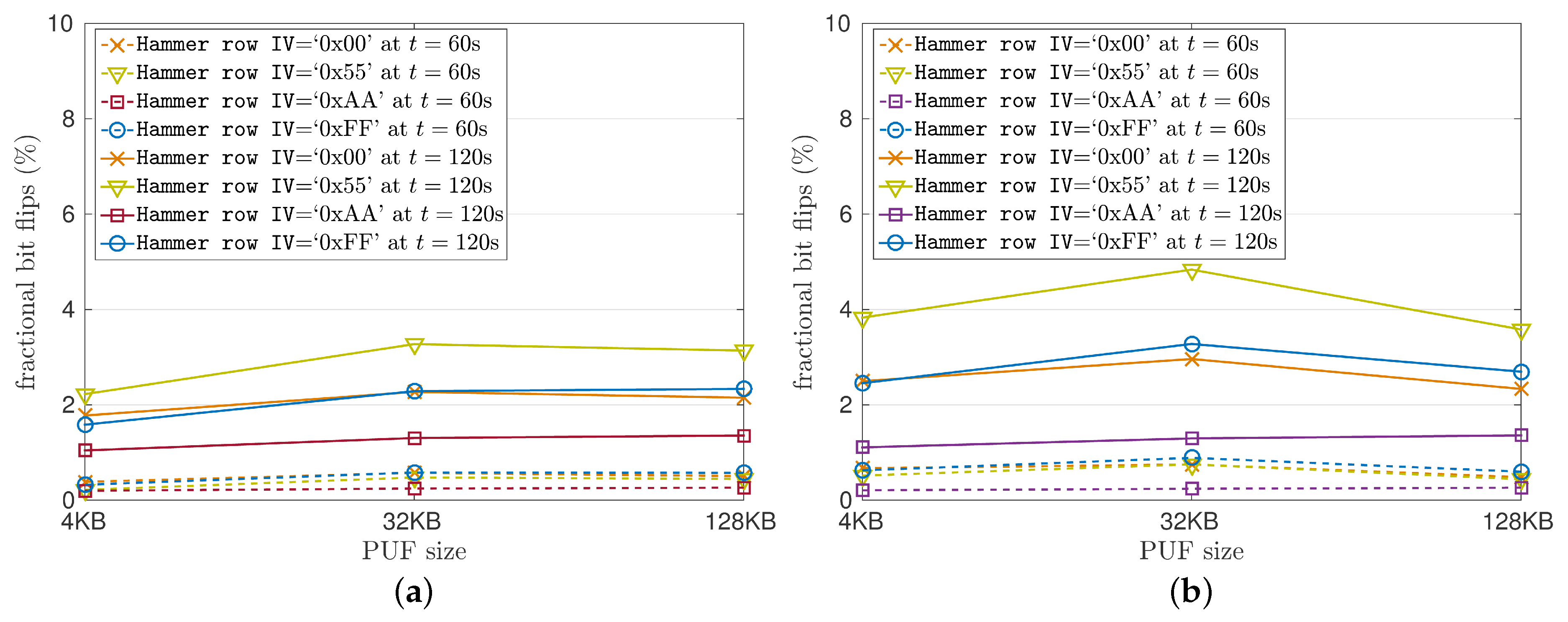
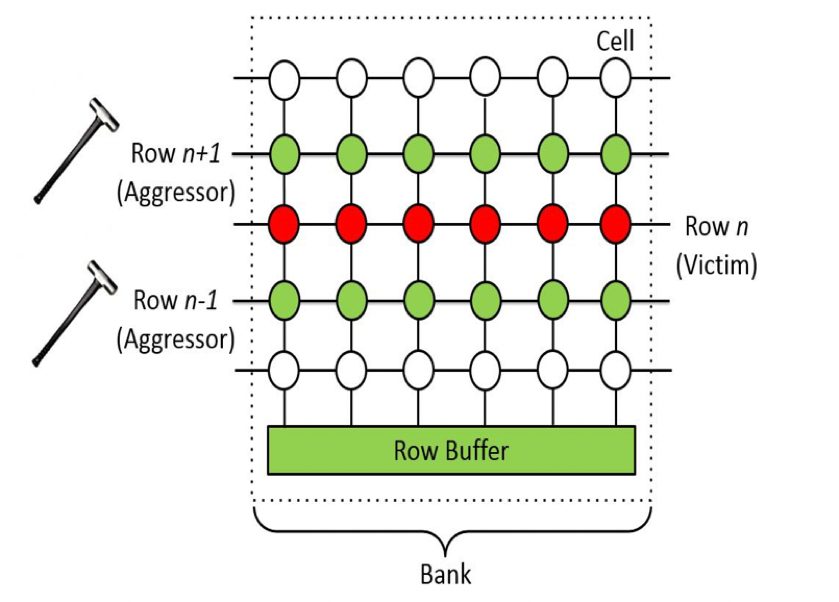
Cryptography | Free Full-Text | Intrinsic Run-Time Row Hammer PUFs: Leveraging the Row Hammer Effect for Run-Time Cryptography and Improved Security † | HTML
PC security facing another “heavy hammer”, Baidu Security discovers a new Rowhammer attack | by Baidu Security X-Lab | Baidu Security X-Lab | Medium
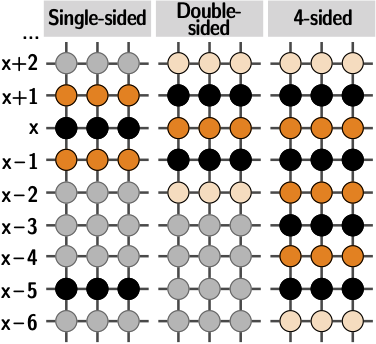
![PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/ec6ca596b8a74e2a2c6a525fb9ccd3476c20eb3e/9-Figure9-1.png)
PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar
![PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/ec6ca596b8a74e2a2c6a525fb9ccd3476c20eb3e/6-Figure4-1.png)
PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar
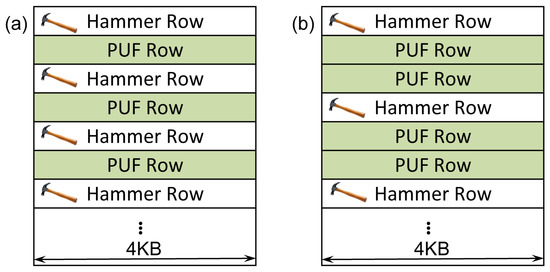
Cryptography | Free Full-Text | Intrinsic Run-Time Row Hammer PUFs: Leveraging the Row Hammer Effect for Run-Time Cryptography and Improved Security † | HTML
Uncovering In-DRAM RowHammer Protection Mechanisms: A New Methodology, Custom RowHammer Patterns, and Implications
![PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/ec6ca596b8a74e2a2c6a525fb9ccd3476c20eb3e/8-Figure7-1.png)
PDF] Revisiting RowHammer: An Experimental Analysis of Modern DRAM Devices and Mitigation Techniques | Semantic Scholar
![Security] How to exploit DRAM with Hammertime (Rowhammer🔨 attack step by step) | by Anna Kim | Medium Security] How to exploit DRAM with Hammertime (Rowhammer🔨 attack step by step) | by Anna Kim | Medium](https://miro.medium.com/max/1400/1*KmoCdrp6GOzpDhN31nBiPQ.png)
Security] How to exploit DRAM with Hammertime (Rowhammer🔨 attack step by step) | by Anna Kim | Medium






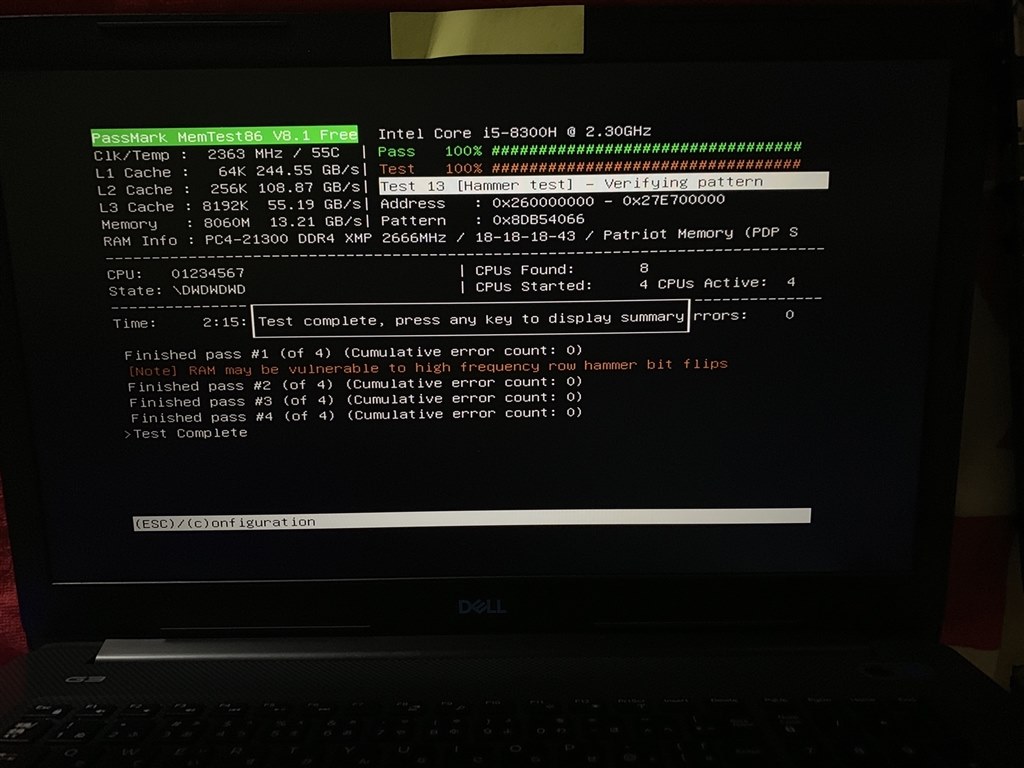
![SOLVED] - How to realiably test the ram stick? | Tom's Hardware Forum SOLVED] - How to realiably test the ram stick? | Tom's Hardware Forum](https://i.imgur.com/3JZFd3i.jpg)